You may have encountered a problem with your Task Sequences that a step to start BitLocker encryption does not work as expected. Depending on a method used to start the encryption (e.g. built-in “Enable BitLocker” step, StartMBAMEncryption.wsf script), the error you are getting varies, but quite often the underlying issue is the same: the TPM chip in the BIOS has not been configured correctly. This might be due to fact that deployment engineer forgot to activate the chip in the BIOS, or because you are running deployment on a machine that was previously encrypted and keys stored in TPM chip have not been cleared. Either way – this article gives you a quick and simple way of making sure Task Sequence covers such scenarios!
In order to achieve that we will leverage Win32_TPM WMI class and PowerShell to call appropriate method. The downside of this approach is this: since we are using PowerShell, this will not work in Windows PE. In other words, if you are using BitLocker pre-provisioning – this won’t help you much and you will have to look at some other imlementation (I have briefly tried to call appropriate method using WMIC with little success, next thing to try would be a VBScript to call upon this). However, if you are initiating encryption in full OS, this solution should work just fine for you.
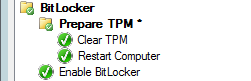
Now, you may feel the post has been slightly mis-advertised – while we need just one step to prepare TPM, we will add three new items to the Task Sequence to neatly cover everything that is necessary!
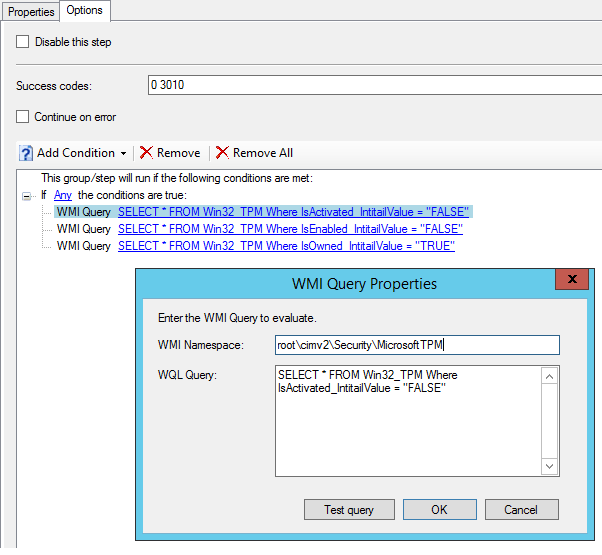
First of all, add a New Group before your step that start actual encryption and call it “Prepare TPM *“. Next, go to Options tab of that group and the below conditions. This is to ensure we only prepare TPM module if it is necessary. In order for encryption to work the first time, the TPM chip must be Activated, Enabled and NOT Owned. We therefore need to prepare the TPM chip if any of these three is not true. First of all, add new If statement and set it to Any. Next, add three WMI queries as listed below. Make sure they all reference root\cimv2\Security\MicrosoftTPM namespace (NOT the default root\cimv2).
SELECT * FROM Win32_TPM Where IsActivated_InitialValue = "FALSE" SELECT * FROM Win32_TPM Where IsEnabled_InitialValue = "FALSE" SELECT * FROM Win32_TPM Where IsOwned_InitialValue = "TRUE"
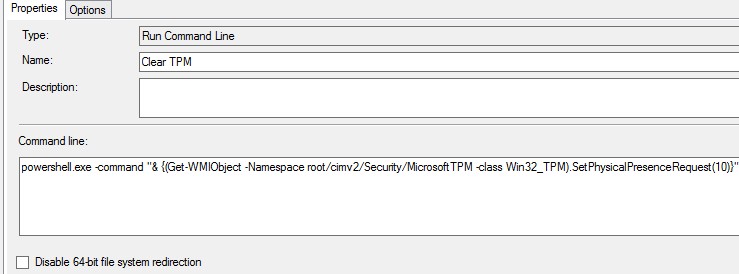
Next, you need to add a new Run Command Line step. Here we are going to call a PowerShell Get-WMIObject cmdlet, reference Win32_TPM class and use it to call SetPhysicalPresenceRequest method. It takes one input argument in a form of a integer – we will use 10, which means Enable, Activate and clear TPM Ownership. You can find more details about it by following the link: https://msdn.microsoft.com/en-us/library/windows/desktop/aa376478(v=vs.85).aspx. So, the command you need to use take the following form:
powershell.exe -command "& {(Get-WMIObject -Namespace root/cimv2/Security/MicrosoftTPM -class Win32_TPM).SetPhysicalPresenceRequest(10)}"
Last, but not least, you need to add a Restart Computer step. The above command sends the request to TPM chip, but a reboot will be required for the changes to take place. IMPORTANT! Depending on your machine make, model, BIOS version and BIOS settings a prompt may appear to press a relevant key to either accept or reject the change. This often can be suppressed by setting an appropriate option in BIOS (and even can be automated in the Task Sequence), however this is outside of scope of this post. Consider yourself warned!
These are steps needed to get the TPM chip into a correct state before starting BitLocker encryption. In principle, your Task Sequence should take a similar shape to the one posted below:
Happy encrypting!
Hi Mietek
Nice post! Your spelling is wrong in the select statements. It should be InitialValue instead of IntitailValue.
/Morten
LikeLike
Posted by Morten Rønborg | 2017-10-10, 13:03Thanks Morten & well spotted. Already fixed.
LikeLike
Posted by Mietek Rogala | 2017-10-10, 13:29I can get the powershell command line to work, at first it was failing because of the ” at the beginning and the end of the query. I try different way to make it works, sometime it will run but it’s not changing the setting in the bios. This is some of the combinations I have tried:
powershell.exe -command “set-excutionpolicy Unrestricted; (Get-WmiObject -Namespace “root\CIMV2\Security\MicrosoftTpm” -Class Win32_TPM).SetPhysicalPresenceRequest(10)”
powershell.exe -executionpolicy bypass -command ‘(Get-WmiObject -Namespace “root\CIMV2\Security\MicrosoftTpm” -Class Win32_TPM).SetPhysicalPresenceRequest(10)’
powershell.exe -command “& {(Get-WMIObject -Namespace root/cimv2/Security/MicrosoftTPM -class Win32_TPM).SetPhysicalPresenceRequest(10)}”
powershell.exe -executionpolicy bypass -command “& {(Get-WMIObject -Namespace root/cimv2/Security/MicrosoftTPM -class Win32_TPM).SetPhysicalPresenceRequest(10)}”
LikeLike
Posted by fred_b | 2018-03-09, 21:40It would be good to confirm these steps succeeded– by adding the opposite criteria to the “Enable Bitlocker” check. For example, a machine without a prepared (or extant) TPM shouldn’t attempt a TPM-Bitlocker step.
Thoughts?
LikeLike
Posted by Christopher Moriarty | 2019-06-17, 17:11This worked for me.
powershell.exe -executionpolicy bypass -command “(Get-WmiObject -Namespace “root\CIMV2\Security\MicrosoftTpm” -Class Win32_TPM).SetPhysicalPresenceRequest(14)”
LikeLike
Posted by Krish M | 2019-10-02, 13:32Reblogged this on system center experts.
LikeLike
Posted by rohitc36 | 2018-11-14, 11:27Hi nice reading your poost
LikeLike
Posted by Jake K | 2025-01-27, 21:59